Active Directory Federation Services (ADFS)
Read time: 4 minutes
Last edited: Nov 20, 2024
Overview
This topic explains how to configure SSO integration between a self-hosted Active Directory Federation Services (ADFS) server and LaunchDarkly.
ADFS is a service provided by Microsoft as a standard role for Windows Server. It provides a web login using existing Active Directory credentials.
If you need information about ADFS errors during configuration, troubleshoot it by accessing the ADFS logs in the Windows Event Viewer.
Prerequisites
To give your organization access to LaunchDarkly through ADFS, you need the following components:
- An Enterprise LaunchDarkly account.
- A signed SSL certificate.
- An Active Directory instance where all users have an email address attribute.
- A Microsoft Server instance with ADFS installed and configured.
This topic does not tell you how to set up ADFS. To learn how to set up ADFS, read Microsoft's documentation.
Set up LaunchDarkly fields
Here is a table explaining LaunchDarkly fields:
| LaunchDarkly field | Notes |
|---|---|
| Sign-on URL | Copy the Token Signing certificate to a Base-64 encoded x.509 file and import it into LaunchDarkly |
| X.509 certificate | Default value: Find the endpoint in Service, then Endpoints. Search for an endpoint with the |
For more information on configuring LaunchDarkly's SSO, read Single sign-on.
Add Relying Party Trust
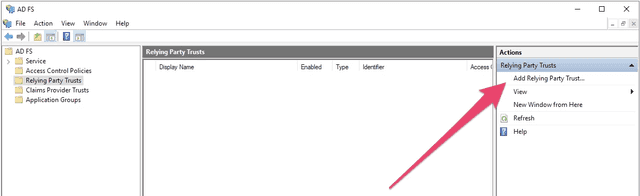
To add the Relying Party Trust:
- Log into the ADFS Management tool.
- Click Add Relying Party Trust.... The Add Relying Party Trust Wizard appears:
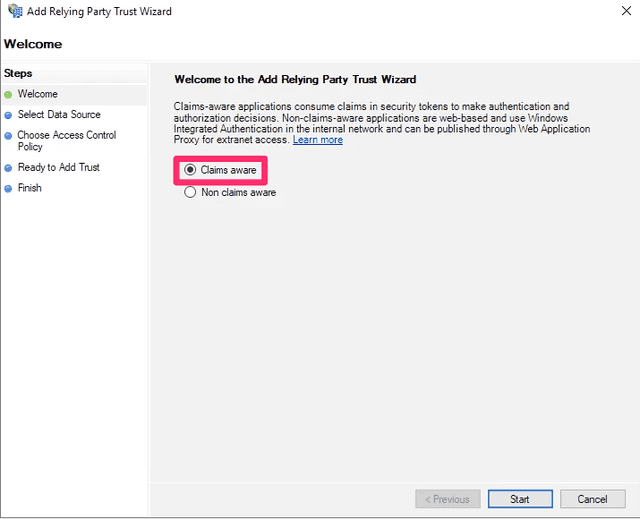
- Click Start. Keep the default value, which is Claims aware:
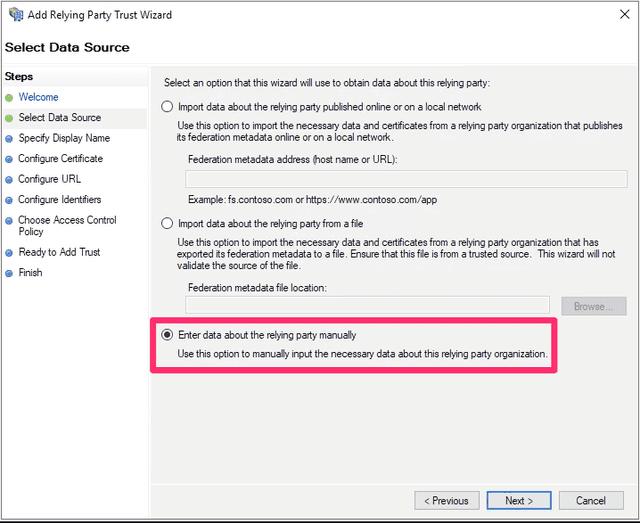
- Choose Enter data about the relying party manually:
- Click Next. The "Specify Display Name" screen appears.
- Set a display name of your choosing.
- Click Next. The "Configure Certificate" screen appears.
- You do not need to choose a certificate. Click Next.
- Select Enable support for the SAML 2.0 WebSSO protocol.
- Enter the Assertion consumer service URL from the SSO section of LaunchDarkly into the Relying party SAML 2.0 SSO service URL field.
- Click Next.
- In the Relying party trust identifier field, enter
app.launchdarkly.com. - Click Add.
- Click Next. The "Choose Access control Policy" screen appears.
- You do not need to change any access control policies. Click Next.
- Review your changes and click Next.
- If you are satisfied with the configuration, click Close.
After you have successfully completed this procedure, a new LaunchDarkly trust will appear in the ADFS Management tool.
Set up claim issuance policies
To set up a claim issuance policy:
- Log into the ADFS Management tool.
- Select the LaunchDarkly Trust.
- Click Edit Claim Issuance Policy... in the menu. The "Edit Claim Issuance Policy" window appears.
- Click Add Rule.
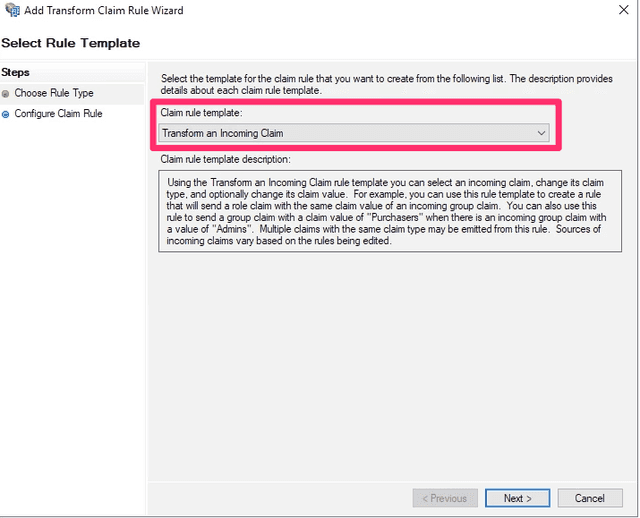
- Set Claim rule template to "Transform an Incoming Claim."
- Click Next:
- Set the following options:
- Claim rule name: Enter a human-readable name, such as "Email to NameID."
- Incoming claim type: E-Mail Address
- Outgoing claim type: Name ID
- Outgoing name ID format: Email
- Select Pass through all claim values.
- Click Finish.
ADFS is now configured with LaunchDarkly.
For more information on claim rules, read Microsoft's Create a Rule to Transform an Incoming Claim.
Configure custom roles
You can map LaunchDarkly custom role attributes to ADFS using a claim issuance policy. To learn more about SSO provisioning for roles and custom roles, read Custom roles.
Before you can map custom role attributes, you must get your ADFS groups. To learn how, read Microsoft's Microsoft's Create a Rule to Send Claims Using a Custom Rule.
Your rule will look something like this:
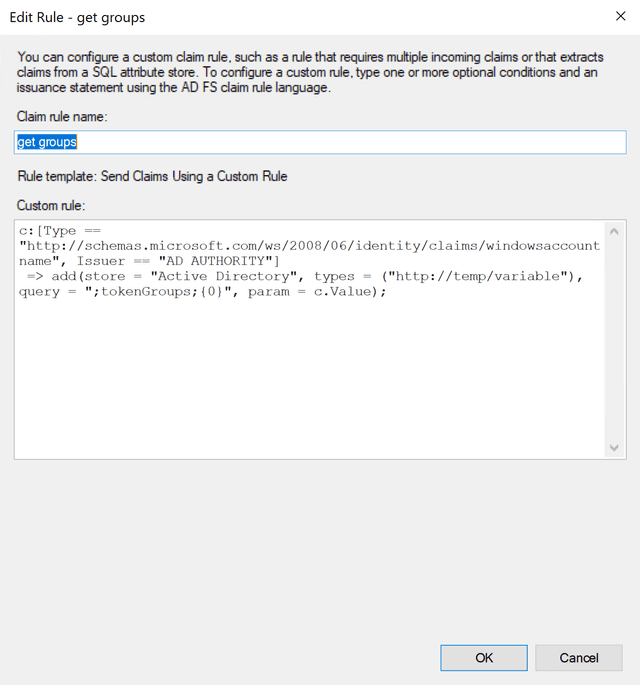
To send claims using a custom rule:
-
Log into the ADFS Management tool.
-
Select LaunchDarkly Trust.
-
Click Edit Claim Issuance Policy... in the menu. The "Edit Claim Issuance Policy" window appears.
-
Click Add Rule.
-
Set Claim rule template to Send Claims using a custom rule.
-
Click Next.
-
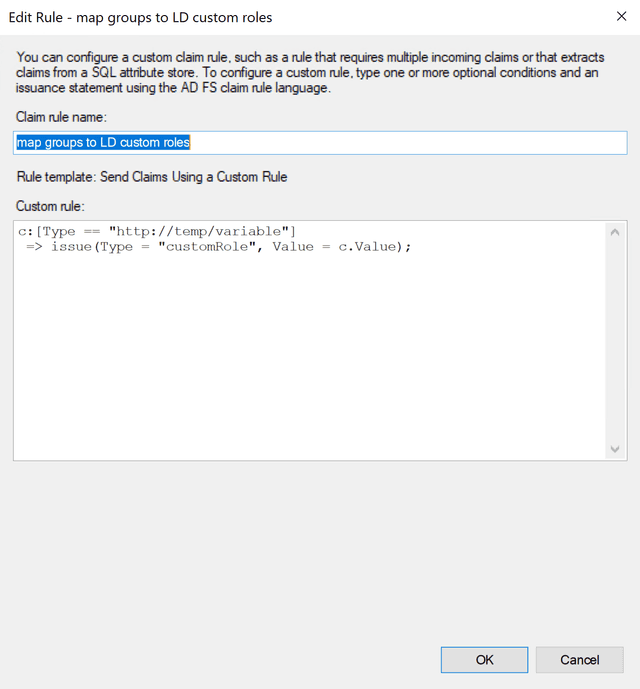
Enter a human-readable name, such as "Map groups to LD custom roles."
-
In the Custom rule window, enter the following:
Here is an image of the custom rule:
- Click OK.
You can now assign ADFS members to custom role groups using the "Member of" tab within user properties.
SAML ignores empty fields if used in Roles or customRoles. To clear all existing roles, enter an empty string "" into the field.
Test drive and enable
After you successfully complete the procedures in this topic, you can log in through ADFS when test-drive mode is enabled. To learn more, read Test-drive mode.
If you are able to successfully log in with test-drive mode enabled, you can enable SSO for the rest of your organization. To learn more, read Single sign-on.